AWS Service VPC¶
For the Centralized (hub) mode deployment using AWS Transit Gateway, the Valtix Gateway is deployed in a new VPC. This VPC is called a Service VPC. The Service VPC and the application (Spoke) VPCs are connected to the AWS Transit Gateway in a Hub-Spoke model as shown below:
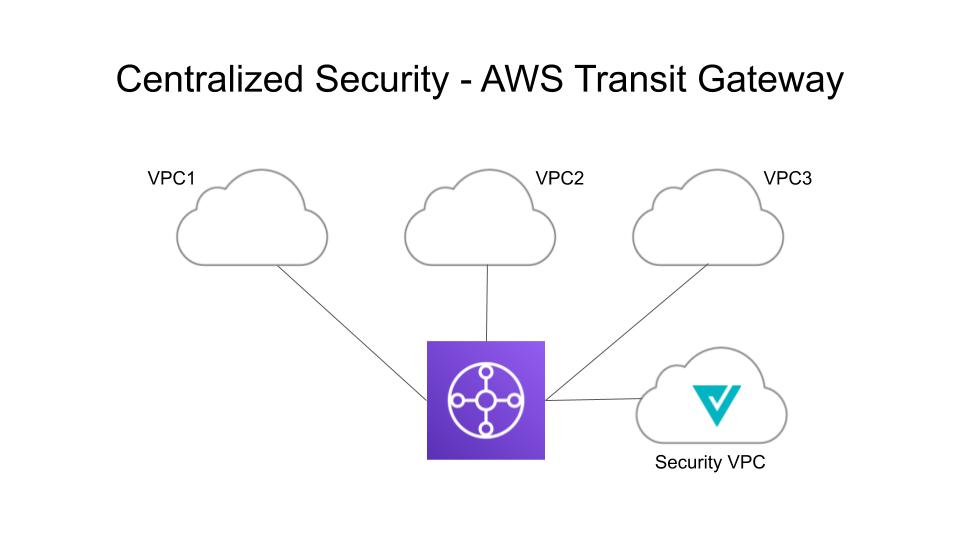
Valtix orchestrates creating the Service VPC, creating (or reusing) the AWS Transit Gateway (TGW), and attaching the Spoke VPCs and the Service VPC to the TGW. It updates the routing between the Service VPC and Spoke VPCs. Customers need to change the route tables associated with subnets in the Spoke VPCs to add a default route and set the destination to the TGW.
Tech Notes
If the TGW is created using the AWS Terraform Provider, the attributes default_route_table_association and default_route_table_propagation MUST be set to "disable".
If the TGW is created using the AWS Console, the attributes Default association route table and Default propagation route table MUST be set to Disable.
If the TGW is created using the Valtix Service VPC orchestration, the attributes are set appropriately.
If these values are not set properly, traffic will bypass the Service VPC and will not be protected by Valtix.
Create a Service VPC¶
- Click Manage -> Service VPCs/VNets
- Click Create VPC/VNet
- Provide a name for the Service VPC (e.g valtix-service-vpc1)
- Select the AWS account
- Select the Region where the Service VPC needs to be created (e.g us-east-1)
- Provide a CIDR block with mask minimum of /25 and maximum of /16. Make sure this does not overlap with any of the spoke VPC CIDRs that you plan to attach to the Transit Gateway (e.g 172.16.0.0/16)
- Select the Availability Zones. It's recommended to select atleast two (2) AZs for HA purposes (e.g us-east-1a and us-east-1b)
- Select a Transit Gateway or create a new one. You can reuse an existing Transit Gateway for all kinds of security types
- Select the Auto accept shared attachments, if you are planning to use the Transit Gateway shared across multiple AWS accounts
- Click Save to create the Service VPC
Tech Notes
- Valtix creates the following resources when a Service VPC is created:
- VPC
- Four (4) subnets in each AZ
- One (1) route table for each of the subnets
- Two (2) security-groups (management and datapath traffic)
- It's required to create a different Service VPC for each of the security types (Ingress, Egress and East-West)
- The Transit Gateway (created/selected during a Service VPC creation) can be reused with other Service VPCs
- Review the Transit Gateway and note that a new TGW (if create new was selected) is created
- A Transit Gateway Attachment to the Service VPC is created
- A Transit Gateway route table is created and associated with the Attachment
- AWS Gateway Load Balancer (GWLB) does not support add/remove of AZs after initial deployment of a GWLB. You will need to redeploy the Service VPC if you need to change AZs.